Popular Reads
Top Results
Can't find what you're looking for?
View all search resultsPopular Reads
Top Results
Can't find what you're looking for?
View all search resultsFury over data breaches: Not if, but when
To be regarded as a personal data breach, a cyberattack or security breach must lead to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, personal data transmitted, stored or otherwise processed. It is clear that a breach is a security incident involving personal data, but not all security incidents (confidentiality, integrity and availability breach) directly become personal data breaches.
Change text size
Gift Premium Articles
to Anyone
I
ndonesian online marketplaces have been on a road of fury in confronting alleged data breaches. One admitted that a security breach occurred but claimed personal data was safe and asked customers not to worry excessively.
Even so, the customers were advised to immediately change their access passwords, activate one-time password or multi-factor authentication features and maintain their trust in the platform’s assurance to protect customer data. Another platform reportedly denied a claimed user data breach (The Jakarta Post, May 8, 2020).
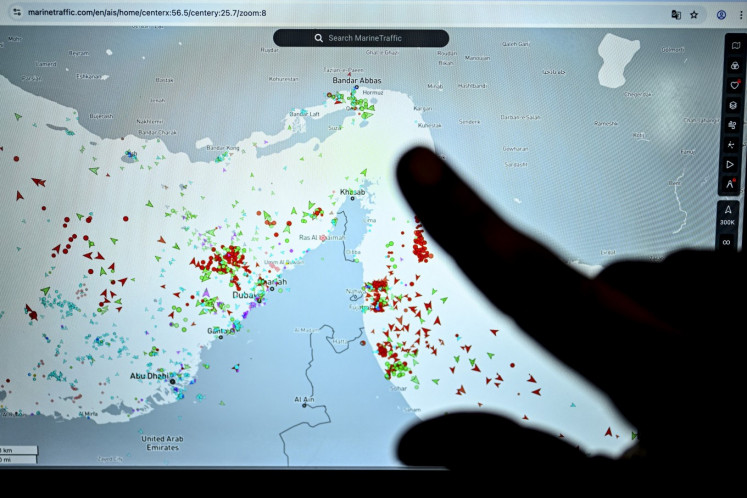
Recently, another online marketplace was exposed for a data breach through a cyberattack in which the offender hacked the computer system for storing customer data, including personal data (email, name, hashed password), and publishing the content in a dark web forum in exchange for US$5,000 for the whole database containing 15 million user account details (the Post, May 5, 2020). On May 6 and 11, the detik.com news portal called our attention to breaches reportedly happening at other online marketplaces.
A breach renders users vulnerable to data theft and produces costs. According to the IBM Security & Ponemon Institute’s 2019 Cost of a Data Breach Report, the average total cost of a data breach incident is $3.92 million, and the average cost per individual record lost or compromised is $150.
To be regarded as a personal data breach, a cyberattack or security breach must lead to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, personal data transmitted, stored or otherwise processed. It is clear that a breach is a security incident involving personal data, but not all security incidents (confidentiality, integrity and availability breach) directly become personal data breaches.
Accordingly, any alleged breach will need to be assessed on a case-by-case basis, including considerations to determine in what situation the data controller (the party that determines the purpose and means of personal data processing; in this case, the platform) can be considered to have become aware of a breach, so that data breach notification requirements shall be fulfilled within 72 hours in accordance with the European Union General Data Protection Regulation (GDPR) or 14 days (for data subject notification) under Indonesia laws (Communications and Information Ministry Regulation No. 20/2016).
For cyber resilience, digital platforms normally do not explain at what time a security incident occurred, but they take proactive measures to effectively implement monitoring of any irregularities and undergo regular evaluation of the electronic system excellence as well as incident response team performance for safeguarding data and guaranteeing information security.